Adaptable. Resilient. Secure.
Secure, resilient wireless mesh systems for high impact teams and individuals.
MIMICK
Remote Hardware Control for Software Developers
Eliminate shipping, travel, downtime, and toil by teleporting your engineers to the hardware. MIMICK closes the distance between your software team and the devices they build for.
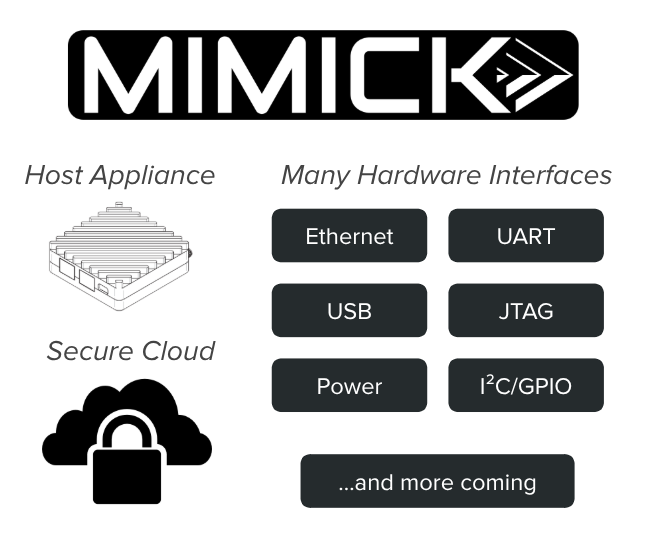
Three components work together to give your team full remote access, automated testing, and provable audit trails — without ever shipping a board.
Raider Product Line
Secure, resilient wireless mesh systems for high impact teams and individuals. We help industry, government, and first responders capture real-world observations for better decision making and smarter automation.
Shadow Shield
A travel router designed for executives, professionals, operators, and other high security minded individuals.
Gate
Ensures seamless and secure communication across multiple networks, including 5G, Wi-Fi HaLow, and other proven mesh network technologies.
Shadow Storm
Low-visibility, RF-shielded, modular laptop platform designed for security-conscious field operations.
Nexus
High performance command and control system in a carry-on-sized, ruggedized Pelican case.
Secure Mesh and Edge Compute
Our products let you do edge collection, processing, and resilient mesh data network solutions for:
Many use cases:
- sensors
- coordinated networks
- control systems
- software
- process automation
- data systems
- electronics
- robotics
- autonomous flight systems
In many locations:
- homes
- farms
- factories
- facilities
- warehouses
- safety
- military
- law enforcement
- and other purposes
With decades of experience, we anticipate edge cases and ensure resiliency and security to minimize failure and downtime.
When should you contact us?
If any of these resonate, let's talk: bd@criticalshift.io
- • You want to collect and move data from many physical sources without requiring public networks.
- • Your team needs to operate where public infrastructure is unreliable or untrusted.
- • You want one device that can work on, and fall back on, several protocols.
- • You need edge collection, processing, and decision making in a single package.
- • You want to add remote command and control.
- • Your hardware team is bottlenecked by shipping, travel, and manual provisioning.
- • You need to provision and test devices remotely at scale.